 Image via Wikipedia
Image via Wikipedia
This is unfortunate for testing reasons, but fortunate for security reasons. It is fortunate because, if an attacker installs a sniffer in a trusted network, but if the trusted network uses a hub to broadcast the packets within that network, then the sniffer would be able to look at every single packet that is going across the network.
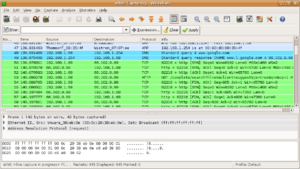
Many network monitoring tools are based on passive packet capture. The principle is
the following: the tool passively captures packets flowing on the network and analyzes
them in order to compute traffic statistics and reports including network protocols being used, communication problems, network security and bandwidth usage. Many network
tools that need to perform packet capture ([tcpdump], [ethereal], [snort]) are based on a popular programming library called libpcap [libpcap] that provides a high level
interface to packet capture.
The main library features are:
• Ability to capture from various network media such as ethernet, serial lines, virtual interfaces.
• Same programming interface on every platform.
• Advanced packet filtering capabilities based on BPF (Berkeley Packet Filtering),
implemented into the OS kernel for better performance.
Depending on the operating system, libpcap implements a virtual device from which
captured packets are read from userspace applications. Despite different platforms
provide the very same API, the libpcap performance varies significantly according to
the platform being used.
On low traffic conditions there is no big difference among the various platforms as all the packets are captured, whereas at high speed1 the situation changes significantly. The following table shows the outcome of some tests performed using a traffic generator [tcpreplay] on a fast host (Dual 1.8 GHz Athlon, 3Com 3c59x ethernet card) that sends packets to a mid-range PC (VIA C3 533 MHz, Intel 100Mbit ethernet card) connected over a 100 Mbit Ethernet switch (Cisco Catalyst 3548 XL) that is used to count the real number of packets sent/received by the hosts3.
The traffic generator reproduces at full speed (~80 Kpps) some traffic that has been captured previously, whereas the capture application is a simple application named pcount based on libpcap that counts and discards, with no further analysis, the captured packets.






